Dynamics
|
Generational Dynamics |
| Forecasting America's Destiny ... and the World's | |
| HOME WEB LOG COUNTRY WIKI COMMENT FORUM DOWNLOADS ABOUT | |
Pakistan blames U.S. drone strike for the 'murder of peace'
This morning's key headlines from GenerationalDynamics.com
 |
Pakistan is calling the U.S. drone strike that killed Pakistani Taliban leader Hakimullah Mehsud a "murder of peace," because it's an attack on the peace process that Pakistan has been pursuing with the terrorist group.
The U.S. has put a $5 million price tag on Mehsud's head because he led of some of the most damaging strikes against U.S. interests by Tehrik-e-Taliban Pakistan (TTP - the Pakistani Taliban). The worst incident was a suicide attack at a CIA base near Khost in Afghanistan in 2009 that killed seven CIA agents and injured six others. The incident was later recreated in the film about the hunt for Osama bin Laden, Zero Dark 30.
However, according to Pakistan's Interior Minister, Chaudhry Nisar:
"Pakistan does not see this strike as an attack on a person, it is an attack on the peace process. Islamabad�s efforts have been ambushed. It was not even an ambush from the front.Seven-week behind-the-scene efforts by us, where brick by brick we tried to roll a process for peace in our homeland, and what have you (US) done? You reduced our weeks-long efforts to ashes hours before a delegation of respected ulema was to leave for Miranshah and hand over a formal dialogue invitation to the Taliban."
Let's be clear that this statement by Nisar is fantasy. This wasn't a "peace process" that was "murdered." Pakistan was about to invite Mehsud to attend negotiations. That's all. As soon as the peace talks were proposed, the Mehsud immediately started to impose conditions: TTP prisoners must be released from jail, the army must be withdrawn from the tribal areas where it has been fighting the Taliban, and the government must agree to impose Sharia law on the country. These conditions could never have been accepted by the Pakistan government. So Nisar's claim is just another totally absurd claim by another politician.
Nisar is demanding that the U.S. end drone strikes. He'd better have a chat with his government's own Inter-Services Intelligence (ISI) agency, which has always worked closely with the U.S. to identify drone strike targets. It's quite likely that the ISI was aware of the strike on Mehsud before it occurred. Daily Times (Pakistan) and VOA and Telegraph
China's aggressive demands in the South China Sea, demanding sovereignty over the entire region, including areas that have historically belonged to other nations, have backfired in the sense that they have had adverse consequences for China:
China has become increasingly isolated, with no "natural allies" in the region besides North Korea and Pakistan. [I would add Cambodia to this list.]
These adverse consequences to China's diplomatic policies do not mean that China will retrench and rethink its aggressiveness. To the contrary, the adversities will make China more nationalistic, and more likely to use military force, instead of diplomatic policies. China seems to be set on a collision course with the United States, Japan and India, and probably Russia as well. South Asia Analysis Group (SAAG)
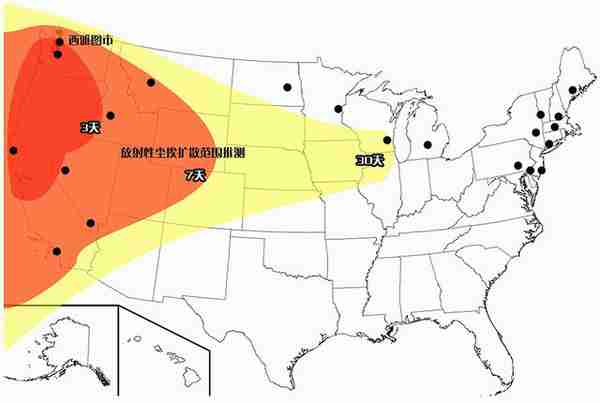 |
China's state-run media are boasting about a submarine fleet capable of launching warheads at cities across the United States. This openness is a major change of policy. According to Chinese military expert Major General Yin Zhuo:
"By showing the world China�s military development, the army hopes to deter those who have ulterior motives. Those who want to challenge China�s core interests: they will not only face its naval aviation forces, but also its underwater submarine forces."
One Global Times article explains the military strategy as follows:
"Because the Midwest states of the U.S. are sparsely populated, in order to increase the lethality, [our] nuclear attacks should mainly target the key cities on the West Coast of the United States, such as Seattle, Los Angeles, San Francisco and San Diego. ...If we launch our DF 31A ICBMs over the North Pole, we can easily destroy a whole list of metropolises on the East Coast and the New England region of the U.S., including Annapolis, Philadelphia, New York, Boston, Portland, Baltimore and Norfolk, whose population accounts for about one-eighth of America�s total residents."
China�s submarine fleet is reportedly the world�s second-largest, with about 70 vessels. About 10 are nuclear-powered, and four or more of those are nuclear ballistic submarines capable of launching missiles. CNTV (Beijing) and Washington Times and Daily Mail (London)
China has for the first time sent 4,000 ton electronic reconnaissance ship to Hawaii, within the U.S. 200-nautical mile EEZ (exclusive economic Zone). The ship is believed to have jamming equipment, and has a potential for offensive actions against the U.S. Global Research
(Comments: For reader comments, questions and discussion, see the 3-Nov-13 World View -- China boasts about submarines capable of attacking cities across U.S. thread of the Generational Dynamics forum. Comments may be
posted anonymously.)
(3-Nov-2013)
Permanent Link
Receive daily World View columns by e-mail
Donate to Generational Dynamics via PayPal
Web Log Summary - 2016
Web Log Summary - 2015
Web Log Summary - 2014
Web Log Summary - 2013
Web Log Summary - 2012
Web Log Summary - 2011
Web Log Summary - 2010
Web Log Summary - 2009
Web Log Summary - 2008
Web Log Summary - 2007
Web Log Summary - 2006
Web Log Summary - 2005
Web Log Summary - 2004
Web Log - December, 2016
Web Log - November, 2016
Web Log - October, 2016
Web Log - September, 2016
Web Log - August, 2016
Web Log - July, 2016
Web Log - June, 2016
Web Log - May, 2016
Web Log - April, 2016
Web Log - March, 2016
Web Log - February, 2016
Web Log - January, 2016
Web Log - December, 2015
Web Log - November, 2015
Web Log - October, 2015
Web Log - September, 2015
Web Log - August, 2015
Web Log - July, 2015
Web Log - June, 2015
Web Log - May, 2015
Web Log - April, 2015
Web Log - March, 2015
Web Log - February, 2015
Web Log - January, 2015
Web Log - December, 2014
Web Log - November, 2014
Web Log - October, 2014
Web Log - September, 2014
Web Log - August, 2014
Web Log - July, 2014
Web Log - June, 2014
Web Log - May, 2014
Web Log - April, 2014
Web Log - March, 2014
Web Log - February, 2014
Web Log - January, 2014
Web Log - December, 2013
Web Log - November, 2013
Web Log - October, 2013
Web Log - September, 2013
Web Log - August, 2013
Web Log - July, 2013
Web Log - June, 2013
Web Log - May, 2013
Web Log - April, 2013
Web Log - March, 2013
Web Log - February, 2013
Web Log - January, 2013
Web Log - December, 2012
Web Log - November, 2012
Web Log - October, 2012
Web Log - September, 2012
Web Log - August, 2012
Web Log - July, 2012
Web Log - June, 2012
Web Log - May, 2012
Web Log - April, 2012
Web Log - March, 2012
Web Log - February, 2012
Web Log - January, 2012
Web Log - December, 2011
Web Log - November, 2011
Web Log - October, 2011
Web Log - September, 2011
Web Log - August, 2011
Web Log - July, 2011
Web Log - June, 2011
Web Log - May, 2011
Web Log - April, 2011
Web Log - March, 2011
Web Log - February, 2011
Web Log - January, 2011
Web Log - December, 2010
Web Log - November, 2010
Web Log - October, 2010
Web Log - September, 2010
Web Log - August, 2010
Web Log - July, 2010
Web Log - June, 2010
Web Log - May, 2010
Web Log - April, 2010
Web Log - March, 2010
Web Log - February, 2010
Web Log - January, 2010
Web Log - December, 2009
Web Log - November, 2009
Web Log - October, 2009
Web Log - September, 2009
Web Log - August, 2009
Web Log - July, 2009
Web Log - June, 2009
Web Log - May, 2009
Web Log - April, 2009
Web Log - March, 2009
Web Log - February, 2009
Web Log - January, 2009
Web Log - December, 2008
Web Log - November, 2008
Web Log - October, 2008
Web Log - September, 2008
Web Log - August, 2008
Web Log - July, 2008
Web Log - June, 2008
Web Log - May, 2008
Web Log - April, 2008
Web Log - March, 2008
Web Log - February, 2008
Web Log - January, 2008
Web Log - December, 2007
Web Log - November, 2007
Web Log - October, 2007
Web Log - September, 2007
Web Log - August, 2007
Web Log - July, 2007
Web Log - June, 2007
Web Log - May, 2007
Web Log - April, 2007
Web Log - March, 2007
Web Log - February, 2007
Web Log - January, 2007
Web Log - December, 2006
Web Log - November, 2006
Web Log - October, 2006
Web Log - September, 2006
Web Log - August, 2006
Web Log - July, 2006
Web Log - June, 2006
Web Log - May, 2006
Web Log - April, 2006
Web Log - March, 2006
Web Log - February, 2006
Web Log - January, 2006
Web Log - December, 2005
Web Log - November, 2005
Web Log - October, 2005
Web Log - September, 2005
Web Log - August, 2005
Web Log - July, 2005
Web Log - June, 2005
Web Log - May, 2005
Web Log - April, 2005
Web Log - March, 2005
Web Log - February, 2005
Web Log - January, 2005
Web Log - December, 2004
Web Log - November, 2004
Web Log - October, 2004
Web Log - September, 2004
Web Log - August, 2004
Web Log - July, 2004
Web Log - June, 2004